4th Edition of the TUM Blockchain&Cybersecurity Salon
Aims
- Exploring core technologies for security, scalability, and privacy in blockchain and cybersecurity systems
- Discussing applications and solutions with requirements met by these core technologies, and to which extent these technologies provide value
- Exchange on methods for assessment of distributed systems, with focus on P2P layer, smart-contract security, and cryptographic innovations
- Extend to intersection of cybersecurity solutions and distributed systems
- Bridge academia, industry, and students and introduce recent topics from various layers of the blockchain stack and cybersecurity
- Introduce current technologies to startups, SMEs, and enterprises to bring research into practice
Topical Scope
- Individual layers of Blockchain Protocols spanning hardware, peer-to-peer network, consensus, execution layers, applications, and ecosystems
- Innovative scalability and privacy technologies, such as zero knowledge proofs or trusted execution environments
- Cybersecurity solutions for AI, access management, identity solutions, …
- Design, verification, and implementation of smart contracts logic
- Methods and tools for performance assessment
- Overview of possible optimization solutions and their applicability to blockchain solutions
- Applications and use-cases of distributed and decentralized systems and their open challenges
- Supply chain security
Organisation by the Technical University of Munich, KTH Royal Institute of Technology, and Instituto Superior Técnico - University of Lisbon
- Chair: Georg Carle
- Organizing committee chairs: Veronika Bauer, Stefan Genchev, Martin Monperrus, Filip Rezabek, Nina Schwanke, and Christof Ferreira Torres
Venue
- 2nd and 3rd June 2026
- TUM-IAS Institute of Advance Studies
Tentative Program
Day 1 - Tuesday 02.06.2026
Get Together - 09:00-09:30 CEST
Session 1 - 09:30-11:00 CEST
Topic: Blockchain Stack Attacks & Verification
Chair:
- Georg Carle (TUM): Welcome and Introduction
- Christof Ferreira Torres (INESC-ID & Instituto Superior Técnico, University of Lisbon): From Predator to Prey: Illuminating Ethereum’s Dark Forest of MEV Bot Exploits
Abstract
Amid the rapid expansion of decentralized exchanges, lending protocols, yield farming, and the tokenization of real-world assets, Maximal Extractable Value (MEV) has quietly developed into a highly profitable domain. What began as a niche phenomenon has matured into a complex ecosystem with multiple intermediaries, each capturing a portion of the value extracted. To date, estimates indicate that more than one billion USD has been generated, largely through the strategic reordering of blockchain transactions. While some MEV practices, such as sandwich attacks, are widely viewed as harmful to users, others, including arbitrage and liquidations, can contribute positively to market efficiency. However, the significant financial incentives have also drawn in a new wave of malicious actors, extending beyond the traditionally studied forms of harmful MEV. These adversaries are typically indifferent to distinctions between “benign” and “harmful” MEV; instead, they opportunistically exploit any vulnerable MEV bot when profit is possible. As a result, MEV bots themselves have increasingly become targets of sophisticated exploitation. In this work, we introduce the first comprehensive taxonomy of attacks against MEV bots and propose a static analysis–driven methodology to identify both direct and indirect attack vectors. Our approach combines Datalog-based analysis with execution simulation, achieving scalability while reducing false positives. Applying this framework, we examine 11,887 MEV bot contracts and identify bytecode-level vulnerabilities susceptible to direct exploitation. In addition, we analyze 463,830 tokens listed on Uniswap, revealing that a notable fraction are deliberately engineered with malicious logic to indirectly target MEV bots. Overall, our findings expose the adversarial nature of the MEV landscape and emphasize the fragile security assumptions underlying many existing MEV extraction strategies.
- Daniel Kales (TACEO): Merces: Private Token Transfers via MPC and CoSNARKs
Abstract
In this talk we present two methods of shielding ERC20 tokens to gain privacy using MPC and Collaborative SNARKs. The first one, dubbed Merces1, focuses on confidential tokens, where balances and transfer amounts remain private while sender and receiver addresses are allowed to leak. The second one, Merces2, takes this approach a step further and additionally hides sender and receiver addresses to achieve a fully private token contract. In both proposals, MPC is responsible for privacy, whereas the ZK proof ensures integrity, even if the MPC servers would collude. In other words, funds can never be misused by the MPC network. Regarding performance: with Merces1 we currently achieve 300 TPS (including proof generation), whereas Merces2 currently achieves around 4 TPS, showing practical feasibility. Both protocols are currently deployed as demos on Base, Arc and Plasma testnet.
- Claudio Di Ciccio (Utrecht University): Leveraging Trusted Execution Environments for Secure and Confidential Process Monitoring
Abstract
Process monitoring techniques enable organisations to gain insights into their business processes by analysing execution records (event logs) stored by information systems. While most efforts in the field focus on intra-organisational scenarios, many real-world business processes span multiple independent organisations (e.g., in a supply chain). Monitoring such collaborative business processes requires integrating event data from various information systems into a unified knowledge base. The transmission of process records across organisational boundaries poses significant challenges to data secrecy and security. Data analysis can reveal information that participating organisations may not consent to disclose to one another or to a third-party hosting process mining services. Consequently, organisations may be reluctant to outsource sensitive data. This talk will present recent advancements in secrecy-preserving inter-organisational process monitoring, with online and offline settings. The presented techniques leverage Trusted Execution Environments (TEEs). TEEs are hardware-protected contexts that guarantee code integrity and data confidentiality before, during, and after their use. Owing to these characteristics, TEEs constitute computing vaults to which information can be securely transferred beyond an organisation’s borders. Computing nodes other than the information provisioners can thus aggregate and elaborate the original, unaltered process data in a secure, externally inaccessible context. The talk will describe architectures and protocols to that end, alongside experiments assessing the performance and scalability of those solutions.
Session 2 - 11:30-13:00 CEST
Topic: Blockchain Scalability, Consensus & Interoperability
Chair: Filip Rezabek (TUM)
- Roger Wattenhofer (Anza/ETH Zurich): Reconstructing the Solana Blockchain
Abstract
Solana is an established high-performance blockchain, but 2026 promises to be a pivotal year for Solana. The Alpenglow consensus update revises core aspects of block production and finality, with implications for latency, throughput, and fault tolerance. Building on this new protocol design, Solana will then offer multiple concurrent proposers to mitigate transaction censorship and improve liveness under adversarial conditions. This talk examines the technical motivations behind these changes, their expected impact, and the economic trade-offs of evolving Solana’s architecture.
- Zeta Avarikioti (TU Wien & Common Prefix): CoBRA: A Universal Strategyproof Confirmation Protocol for Quorum-based Proof-of-Stake Blockchains
Abstract
The security of many Proof-of-Stake (PoS) payment systems relies on quorum-based State Machine Replication (SMR) protocols. While classical analyses assume purely Byzantine faults, real-world systems must tolerate both arbitrary failures and strategic, profit-driven validators. We therefore study quorum-based SMR under a hybrid model with honest, Byzantine, and rational participants. We first establish the fundamental limitations of traditional consensus mechanisms, proving two impossibility results: (1) in partially synchronous networks, no quorum-based protocol can achieve SMR when rational and Byzantine validators collectively exceed 1/3 of the participants; and (2) even under synchronous network assumptions, SMR remains unattainable if this coalition comprises more than 2/3 of the validator set. Assuming a synchrony bound Δ, we show how to extend any quorum-based SMR protocol to tolerate up to 1/3 Byzantine and 1/3 rational validators by modifying only its finalization rule. Our approach enforces a necessary bound on the total transaction volume finalized within any time window Δ and introduces the \emph{strongest chain rule}, which enables efficient finalization of transactions when a supermajority of honest participants provably supports execution. Empirical analysis of Ethereum and Cosmos demonstrates validator participation exceeding the required 5/6 threshold in over 99 of blocks, supporting the practicality of our design. Finally, we present a recovery mechanism that restores safety and liveness after consistency violations, even with up to 5/9 Byzantine stake and 1/9 rational stake, guaranteeing full reimbursement of provable client losses.
- Yvonne-Anne Pignolet (StableClear): The Trust Spectrum: Architectures for Non-Custodial Multi-Chain Swaps
Abstract
When we trade assets across different blockchains, it’s crucial to consider who we trust with our money during the process? In this talk, we explore the “Trust Spectrum” of settlement architectures. We’ll look at how to build a neutral Financial Market Infrastructure. I will share the architectural journey of StableClear, comparing three different ways to handle cross-chain settlement. Moreover, we will discuss the design principles required to ensure users keep control of their assets at all times, making the infrastructure “non-custodial” as well as the technical trade-offs required to build a safer, more transparent foundation for the future of finance.
Lunch Break - 13:00-14:15 CEST
Session 3 - 14:15-14:55 CEST
Panel Discussions
Moderator: Eomji Park (Encode Club)
- Panelists
- Topics
- Connecting Academia and Industry
- Bridging Theory and Protocol Design
- Acedamia vs industry, or both?
Session 4 - 15:00-15:45 CEST
Poster Madness
Chair: Veronika Bauer (TUM)
Presentation of posters.
Coffee Break
Session 5 - 16:15-17:45 CEST
Topic: Cybersecurity Automation and Supply Chain Security
Chair: Christof Ferreira Torres (INESC-ID & Instituto Superior Técnico, University of Lisbon)
- Martin Monperrus (KTH Royal Institute of Technology): Software Supply Security of Web3
Abstract
Web3 applications, built on blockchain technology, manage billions of dollars in digital assets through decentralized applications (dApps) and smart contracts. These systems rely on complex, software supply chains that introduce significant security vulnerabilities. This paper examines the software supply chain security challenges unique to the Web3 ecosystem, where traditional Web2 software supply chain problems intersect with the immutable and high-stakes nature of blockchain technology. We analyze the threat landscape and propose mitigation strategies to strengthen the security posture of Web3 systems.
- Yannis Smaragdakis (Dedaub/University of Athens): Static Analysis for Smart Contract Decompilation and Verification
Abstract
The will give a quick overview of the techniques that underpin the Dedaub decompiler for EVM smart contracts as well as the security analyzer that has led to many vulnerability discoveries (e.g., 11 large bug bounties of over $3M total). The backdrop of both technologies is context-sensitive static analysis, a model that allows tunable precision of program reasoning. The talk will illustrate the actual algorithms, which vary significantly per application domain.
- Kaihua Qin (University of Warwick): Talk about usage of AI for Blockchain Attacks
Session 6 - 17:45-18:25 CEST
Panel Discussions
Moderator: Filip Rezabek (TUM)
- Topics
- Turning Research into Ventures
- Collaborative Research Models
- Aligning Incentives
Day 2 - Wednesday 03.06.2026
Get Together - 09:00-09:30 CEST
Session 7 - 09:30-11:15 CEST
Topic: MEV, DeFi & Mechanism Design
Chair: Christof Ferreira Torres (INESC-ID & Instituto Superior Técnico, University of Lisbon)
- Georg Carle (TUM): Welcome and Introduction
- Lioba Heimbach (Category Labs): Blockspace Under Pressure: An Analysis of Spam MEV on High-Throughput Blockchains
Abstract
On high-throughput, low-fee blockchains, a qualitatively new form of maximal extractable value (MEV) has emerged: searchers submit large volumes of speculative transactions, whose profitability is resolved only at execution time. We refer to this as spam MEV. On major rollups, it can at times consume more than half of block gas, even though only a small fraction of probes ultimately results in a trade. Despite growing awareness of this phenomenon, there is no principled framework for understanding how blockchain design parameters shape its prevalence and impact.
We develop such a framework, modeling spam transactions competing for on-chain opportunities under a competitive equilibrium that drives their profits to zero, and deriving equilibrium spam volumes as a function of block capacity, minimum gas price, and the transaction fee mechanism. Empirical evidence from Base and Arbitrum supports the model: spam grew sharply as block capacity was scaled up and fell when minimum gas prices were introduced. Our analysis yields three main insights. First, spam is always costly: when block capacity is scarce, it displaces users and drives up gas prices; as block capacity grows, it increasingly consumes execution resources, raising network externality, i.e., the cost of provisioning and processing blocks. We show that spam takes an increasing share of each additional unit of block capacity, so capping it before all users are included creates a favorable trade-off: forgoing a small amount of user welfare eliminates disproportionate spam and externality. Second, we extend the analysis to priority fee ordering and show that ordering transactions by gas price helps reduce spam, as spammers must pay more to reach early block positions. Third, as user demand grows and blockspace is scaled accordingly, spam’s share of block capacity plateaus rather than growing indefinitely.
- Burak Öz (Technical University of Munich & Flashbots): The Price of Decentralization in Block Building
Abstract
We study the decentralized block-building process as a coverage game, with information sources acting as resources from which builders collect transactions to include in their proposed blocks. A builder’s location relative to an information source determines the probability that a transaction emitted by that source is received before the block deadline. At each block construction round, builders simultaneously choose where to locate. We show that the lack of coordination among builders leads to over-concentration at the same regions, causing redundant transaction coverage and welfare losses relative to the optimal placement chosen by a social planner.
- Akaki Mamageishvili (Offchain Labs): TimeBoost: Do Ahead-of-Time Auctions Work?
Abstract
We study the performance of the TimeBoost auction, by comparing cumulative fixed time markout of fast lane trades over the TimeBoost interval to bids for the fast lane. Such comparison allows to assess how well bids predict future extracted value from the time advantage. The correlation between winning bids and markouts is weak across bidders, suggesting that bids are a noisy predictor of extracted value. The correlation slightly improves when comparing paid bids (the second highest bid) instead of winning bids to markouts, which we attribute to the fact that the auction is more of a common value type. In all settings, the relative order of the most frequent bidder performance remains the same, together with their absolute profits. Bids and markouts aggregated over long time intervals exhibit much higher correlation, indicating that bidders detect trends much better than identify when the high arbitrage value is exactly available. One possible explanation for this is the fact that the correlation between previous minute markouts and current minute bids is significant, suggesting that the previous minute markouts is used to predict the next minute value when bidding.
- Christoph Schlegel (Flashbots): Just-in-Time Resale in an Ahead-of-Time Auction: An Event Study
Abstract
We study Arbitrum’s Timeboost mechanism following the adoption of Kairos by its main users – Wintermute and Selini Capital – to understand how the emergence of a just-in-time secondary market affects the dynamics of an ahead-of-time primary auction. We find that competition in the primary auction declines significantly and that Arbitrum captures a smaller share of the value generated around Timeboost. After the transition, paid bids in the primary auction correspond to only 14.8% of the highest bid (compared with nearly 62.7% in the \textit{Pre-Kairos} era) and to a smaller share of searcher profit-and-loss (PnL), even though total PnL remains of similar magnitude across regimes. While the exact distribution of the remaining surplus between searchers and Kairos remains unclear, the evidence suggests that a substantial share is no longer captured through the primary auction. More broadly, our findings suggest that ahead-of-time allocation mechanisms may be particularly vulnerable to secondary-market intermediation when competition among dominant participants is weak. We conclude by outlining possible ways for Arbitrum to improve revenue capture and discussing how these lessons may apply to Ethereum L1.
Session 8 - 11:30-13:00 CEST
Topic: Privacy, Cryptography & Quantum Threats
Chair: Georg Carle (TUM)
- Jonathan Passerat-Palmbach (Flashbots & Imperial College): Talk about FHE
- Filip Rezabek (TUM): Talk about TEE
- Mahdi Sedaghat (Soundness Labs/KU Leuven): Post-Quantum Readiness in Blockchain Abstract
Most blockchains use elliptic curve signatures (ECDSA, EdDSA) in execuation layer, which break under a strong quantum adversary. Exposed public keys today could enable future signature forgeries. This talk presents a practical way to make wallets post-quantum secure without moving assets or hard forks. We start from our FC’26 result: a proof-of-seed construction where the seed phrase, protected by a hash, acts as a quantum-safe anchor. A zero-knowledge proof links this seed to the on-chain account via a smart contract, no new keys, no migration. We then extend this idea to ECDSA chains (e.g., Bitcoin, Ethereum) using BIP39/BIP32, outlining a concrete wallet-level upgrade path and practical deployment patterns across smart contracts, client-side proving, and custody setups.
Lunch Break - 13:00-14:00 CEST
Session 9 - 14:00-14:40 CEST
Panel Discussions
Moderator: Eomji Park (Encode Club)
- Panelists
- Topics
- From TUM to industry
- Relevant topics for work
Session 10 - 14:45-16:00 CEST
Topic: Building Trust and Security Services
Chair: Georg Carle (TUM)
- Stefan Genchev (TUM): Talk about Trust Center and Secure Hardware
- Markus Rudy (Edgeless Systems): Remote Attestation of Distributed Services Abstract
Confidential computing is available on most modern hardware and CVMs can be ordered at most larger cloud providers. The big issue adopters are facing today is how to use these hardware primitives to establish trust in a remote system, especially when they are distributed. This talk is going to present Contrast, a Kubernetes runtime that schedules pods as confidential micro-VMs, and how it can help simplify reference value calculation and transitive verification of workloads, even for third parties and end users.
- Veronika Bauer (TUM): Talk about ZK and TEEs
Wrap-up of the Blockchain&Cybersecurity Salon
Poster Sessions
- Antoine Breton: Secure Execution of WebAssembly Workloads Using TEE
- Eber Christer: Empirical Analysis of Validator Performance in Solana
- José Afonso Teixeira: Post-Quantum Cryptography in Intra-Vehicle Networks
- Jonas Gebele: Semantic Non-Fungibility and Violations of the Law of One Price in Prediction Markets
- Till Koebele: Assessment of I/O in Blockchain Systems
- Yudhistira Wibowo: Assessment of Succinct proofs for TEE Attestations
- Nina Schwanke: Cybersecurity Polygon Program
- TBD: TUM Blockchain Club
Speakers overview

Christof Ferreira Torres
Assistant Professor
INESC-ID & Instituto Superior Técnico, University of Lisbon

Daniel Kales
TACEO
Panelists
Organizing committee

Christof Ferreira Torres
Assistant Professor
INESC-ID & Instituto Superior Técnico, University of Lisbon
Registration
- The number of spots for on-site participations are limited.
- Registration form for audience: Google form
- Speakers use seperate form provided by the organizational team.
Venue - Institute of Advanced Studies, Garching Campus of TUM
Address: Lichtenbergstraße 2a, 85748 Garching bei München, Germany
- 2&3 June - Faculty club, fourth floor

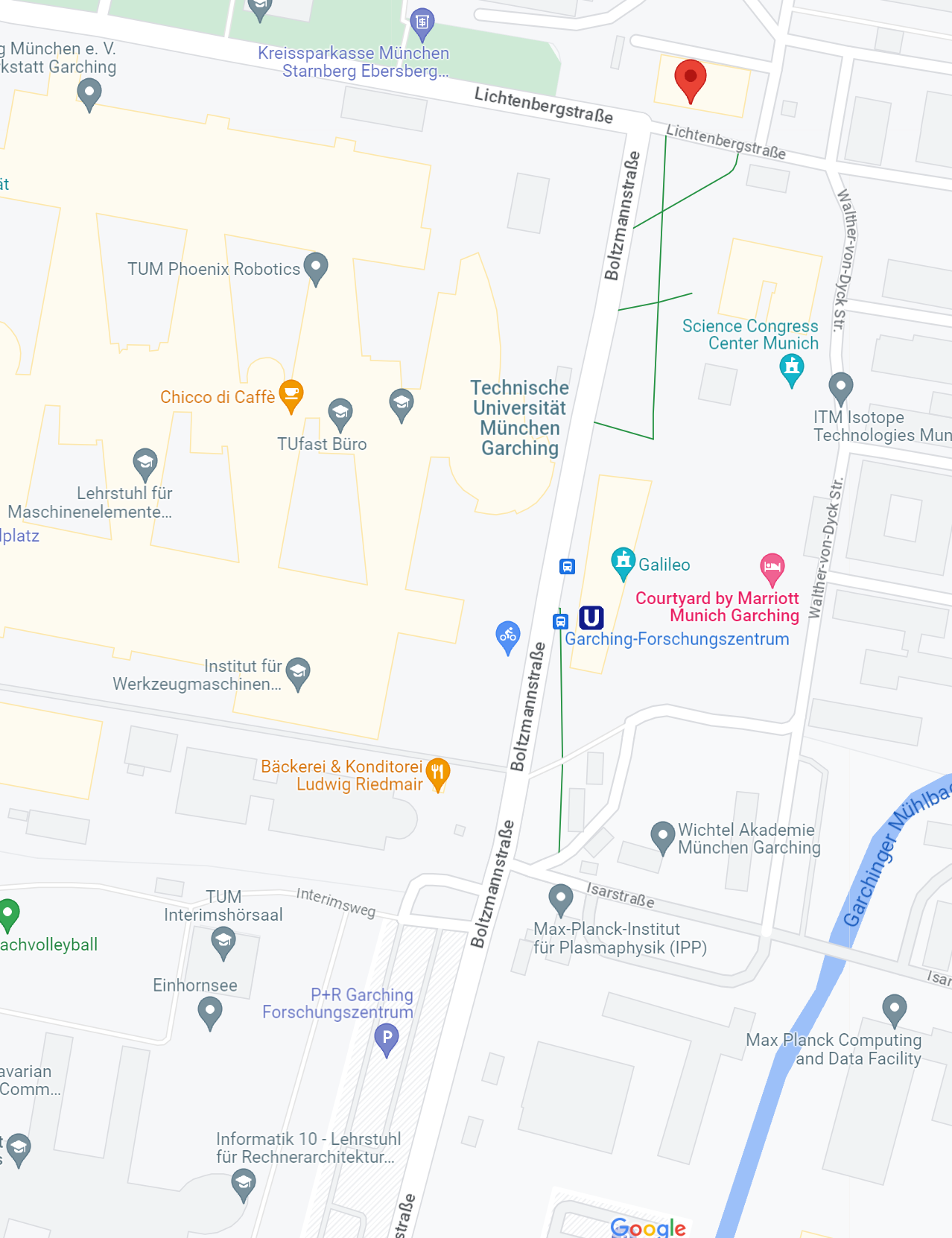
Transport
- Subway U6 - Garching Forschungszentrum
- Possible to arrive with a car - free parking on
- For other inqueries contact the Organizing committee chairs
Knowledge Partner